Recap: 2021 DeFi Security Incidents — Over $657M in Funds Lost
Unlike previous years when the market would be shaken by major centralized exchange hacks, as decentralized finance (DeFi) rapidly developed and became one of the main drivers of the market, hackers' attention has shifted. DeFi thefts have become the new fear gripping the crypto market. A wildly growing market filled with unaudited smart contracts and cloned code has become a go-to cash cow for hackers, with multi-million dollar heists becoming the norm — DeFi has become the hackers' personal ATM.
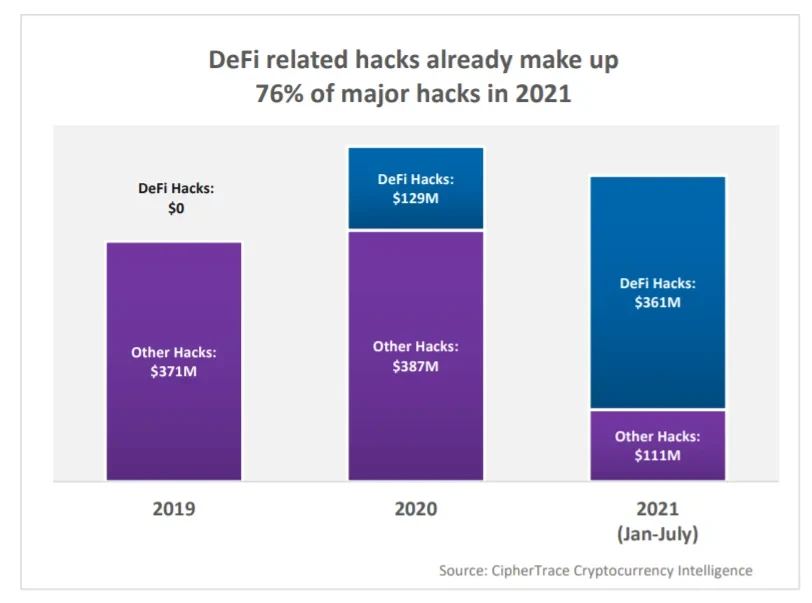
Blockchain analytics firm CipherTrace pointed out in its latest Crypto Asset Crime and Anti-Money Laundering Report that as of the end of July, DeFi-related hacking incidents had cost users $361 million. According to Coin98 data, Q3 2021 saw 11 major DeFi theft incidents, with 5 involving cross-chain bridge asset theft. Excluding July's incidents, August saw 3 incidents with total funds of $296 million (Note: As of publication, the hacker attacking the Poly Network protocol had returned $342 million in tokens). Therefore, from the start of the year, hackers have stolen at least $657 million from DeFi.
As the DeFi ecosystem continues to grow, such incidents will persist. Clearly, DeFi hacking has become another "dark forest" — what are their primary tactics? And how should we respond?
Hacker Created the Biggest Heist in Crypto History "For Fun"
On August 10th, the largest theft in DeFi history occurred when cross-chain protocol Poly Network was attacked, dealing a heavy blow to O3 Swap users of the protocol. According to the on-chain browser, in just over 30 minutes, the hacker walked away with a total of $610 million in crypto assets, including 302 million USDT, 55,000 Ethereum, and 2,000 Bitcoin, among other tokens.
How devastating was this loss? CipherTrace pointed out in its latest report that DeFi hacking losses for all of 2020 totaled $129 million — the Poly Network attack alone was 4.7 times that amount.
Poly Network is a cross-chain interoperability protocol used for trading on decentralized exchanges (DEXs). It was once considered the best implementation of true heterogeneous cross-chain. According to analysis by the Chengdu链安 team, the attacker exploited a logic flaw in the Eth Cross Chain Manager contract. By calling the putCurEpochConPubKeyBytes function in the Eth Cross Chain Data contract through this contract, the attacker changed the Keeper to their own address and then used that address to sign transactions for token withdrawals, draining the large amounts of tokens locked in the Lock Proxy contract.
According to Chengdu链安, the main cause of this attack was a flaw in the contract permission management logic. Any user could call the verifyHeaderAndExecuteTx function to execute transactions, and during internal call operations, function names could be user-controlled, allowing malicious users to abnormally invoke certain functions by carefully constructing data. Additionally, the Eth Cross Chain Manager contract had permission to modify the Keeper — normally changed through the changeBookKeeper function — but in this attack, the attacker successfully modified the Keeper address by crafting data through the call in the verifyHeaderAndExecuteTx function. Since the Keeper address could sign transactions, the largest-loss DeFi attack in history was born.
Given the eye-popping $610 million involved, all major platforms responded actively after the incident, attempting to prevent the hacker from leveraging platform features to launder the stolen funds. OKLink also worked within compliance bounds to share attacker information with security teams, buying precious time for tracking the hacker.
Perhaps pressured by external forces, or perhaps because the hacker themselves claimed "they just launched the attack for fun," the hacker began returning assets. As of publication, the hacker had returned $342 million worth of stolen assets.
OKLink data shows that DeFi grew from $660 million on January 1, 2020 to over $110 billion today — an increase of nearly 175x in just 1 year and 8 months. As of August 12th, the current total value locked (TVL) in DeFi stands at $115.9 billion, compared to $113.57 billion before the May 19th crash — meaning after three months, DeFi's TVL surpassed its pre-crash high, setting a new all-time record.
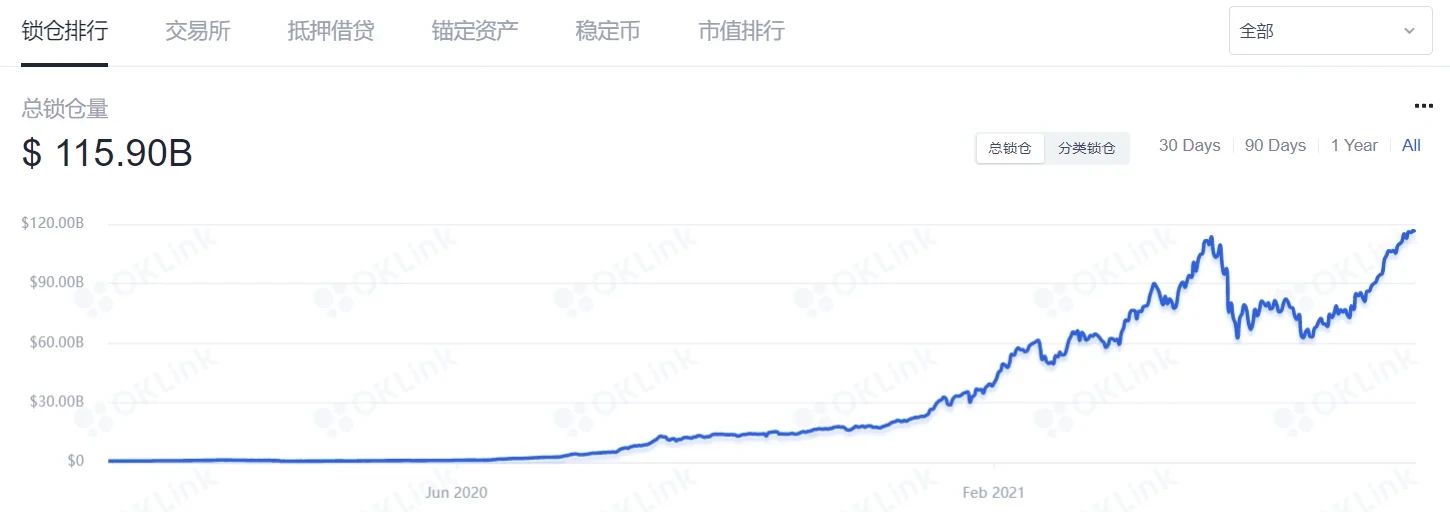
CoinGecko data shows the current total DeFi market cap is $110.327 billion, up 402% from $21.957 billion at the start of the year. But compared to the all-time high of $149.667 billion on May 12th, the market cap has shrunk by 26%. Meanwhile, Bitcoin's current market cap is $857.661 billion, down 38% from its all-time high of $1,187.737 billion — showing that in this market recovery, DeFi has overall outperformed Bitcoin.
As the saying goes, the bigger the funds, the bigger the risk. DeFi's rapid growth and massive capital base, combined with wildly varying quality among on-chain projects, have made it a prime target for hackers.
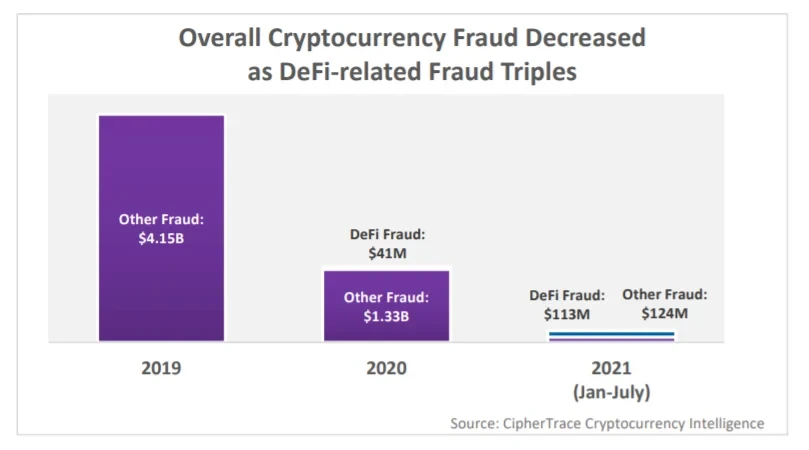
CipherTrace's report noted that as of the end of July 2021, the total funds involved in crypto asset thefts, hacker attacks, and fraud stood at $681 million — a significant decrease compared to $4.5 billion in 2019, suggesting that after two years of market development, the crypto market has made significant upgrades to security systems, user crypto education has improved, and awareness of identifying crypto scams has strengthened.
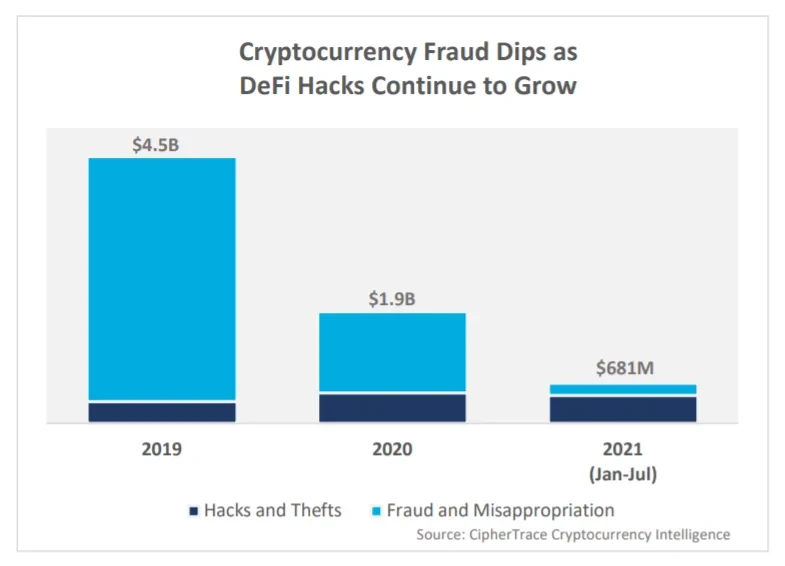
However, it's worth noting that DeFi-related hacker attacks and fraud are on the rise. As of the end of July, hacker attacks had cost DeFi users $361 million, accounting for 76% of total hacking proceeds ($472 million) year-to-date. This $361 million figure is also 2.8 times the amount lost in DeFi hacks throughout 2020.
Additionally, DeFi-related fraud involved $113 million in funds. While overall crypto asset fraud has declined, DeFi fraud has nearly tripled compared to $41 million the previous year. This underscores that DeFi-related hacker attacks, thefts, and fraud incidents definitely warrant attention and vigilance.
DeFi Attacks Proliferate — Flash Loans Are One Common Tactic
In the summer of 2020, the DeFi concept that had been dormant for years erupted in just a few short months. Whether measured by user base or capital attracted, DeFi has since grown into a formidable force in the crypto market. This new赛道 has brought fresh opportunities for investors and entrepreneurs alike, but it has also inevitably provided bad actors with opportunities to exploit the system.
According to incomplete statistics, from last year to this year, DeFi has experienced at least 60+ security incidents. Among these, two attack methods are most common: Rug Pulls and flash loan attacks.
A Rug Pull refers to cryptocurrency developers withdrawing support, draining a DEX liquidity pool, or suddenly abandoning a project and vanishing with investors' funds without warning. Rug Pulls occur predominantly on DEXs and represent a classic DeFi scam. Scammers inject large amounts of funds into a liquidity pool and post enticing ads on social media to attract investors. Once investors deposit their tokens into these pools, the scammers "pull the rug out" by withdrawing all the tokens from the pool.
Next, let's focus on flash loans. According to available records, a flash loan is a type of loan that requires no collateral, with borrowing and repayment completed within the same block. It's important to note that flash loans themselves are merely a tool — neither good nor bad. However, since flash loans frequently appear in news related to DeFi implosions, many uninformed people mistakenly view flash loans as accomplices to malicious attackers — this is a misreading of flash loans.
In fact, flash loans could even be considered a great innovation in smart contracts. Due to structural flaws in DeFi, most collateralized lending protocols require users to over-collateralize assets, resulting in very low capital efficiency. The emergence of flash loans has significantly reduced capital costs — users can access massive funds with virtually no collateral, paying only a tiny fee (e.g., flash loan fees on AAVE are as low as 0.09%), making them useful for arbitrage, collateral swaps, and self-liquidation.
So why do flash loan attacks happen? Attackers simply leverage the characteristics of flash loans — borrowing funds, trading, depositing, and borrowing again on a massive scale within a short period. This allows them to artificially manipulate the price of specific crypto assets on a particular DEX, profiting from the manipulation. In other words, the attacker's operations within the flash loan process itself are technically compliant, but the outcome — damaging the fairness of smart contracts and harming other users' interests — is what makes it an attack.
In 2021 year-to-date, multiple malicious attacks using flash loans have indeed occurred. For example, in February, an attacker launched a flash loan attack on the DeFi lending protocol Alpha Homora, resulting in $37 million being stolen. In an Alpha Homora V2 pool, the attacker borrowed and lent millions of stablecoins, inflating their value and reaping enormous profits. As DeFi matures, substantial liquidity may be the primary factor in reducing flash loan attack risk. Security audits of smart contracts also serve as a second line of defense for vulnerable or misconfigured contracts. Additionally, some projects have launched bug bounty programs.
Recently, there was market chatter that institutional investor interest was shifting from Bitcoin to Ethereum and DeFi. Some projects moved quickly to launch institutional DeFi platforms. While everyone eagerly awaited institutional entry and a new "DeFi Summer," such a major incident broke out. This hack may cause institutional investors to reassess their confidence in DeFi investments. But we also see that DeFi is not standing still — compared to last year, it has made significant breakthroughs across all areas. As DeFi flourishes, we witness not only innovative new financial development paths and the relentless efforts of pioneering entrepreneurs, but also continuously upgrading DeFi security.
While hacker attacks and cybercrime can never be completely eradicated, every attack is also an opportunity for DeFi protocols to reflect and enhance security. Admittedly, for ordinary users, entering the DeFi world does present a certain barrier to entry. But thankfully, everything is evolving — no revolution or transformation happens overnight, and DeFi is no exception.
Disclaimer
This article may contain product-related content not applicable to your region. This article is intended to provide general information only and does not accept responsibility for any factual errors or omissions. This article represents the author's personal views only and does not represent the views of OKX. This article is not intended to provide any advice, including but not limited to: (i) investment advice or investment recommendations; (ii) offers or solicitations to buy, sell, or hold digital assets; or (iii) financial, accounting, legal, or tax advice. Holdings in digital assets (including stablecoins) involve a high degree of risk and may fluctuate significantly, or even become worthless. You should carefully consider whether trading or holding digital assets is appropriate for you based on your financial situation. For questions about your specific circumstances, please consult your legal/tax/investment professional. Any information in this article (including market data and statistics, where applicable) is provided for general reference purposes only. Although all reasonable precautions have been taken in preparing such data and charts, we accept no responsibility for any factual errors or omissions expressed herein. © 2025 OKX. This article may be reproduced or distributed in its entirety, or excerpts of 100 words or less may be used, provided that such use is non-commercial. Any reproduction or distribution of the full article must prominently state: "This article is copyrighted © 2025 OKX, used with permission." Permitted excerpts must cite the article title and include attribution, e.g., "Article title, [author name (if applicable)], © 2025 OKX". Portions of this content may have been generated or assisted by artificial intelligence (AI) tools. Derivative works and other uses of this article are not permitted.
Show More
Recommended Reading

2025 KOL Most Used OKX Products Ranking
In the cryptocurrency industry, professional players' choices are always direct and clear-cut. In 2025, KOLs cast the most authentic votes for industry tools and ecosystem development with their year-long capital investment and time commitment. Revolving around four core questions — "What was your biggest achievement this year?", "With that achievement in mind, what OKX products did you use most and love most in 2025?", "Why do you love it?", "What...
2026年1月5日

2026 Investment Outlook: Asset On-Chain, Intelligence & Privacy | OKX Year in Review
The three major trends shaping crypto's future: asset transformation, entity transformation, and rule transformation. As we stand on the cusp of 2026, after four years of focused "road-building" infrastructure, the crypto industry is experiencing a profound paradigm shift. OKX Ventures defines this as the dawn of the "Kinetic Finance" era — where the core is no longer how fast the network is, but the flow and monetization of on-chain assets.
2025年12月31日

Vote with Data — A Deep Dive into 2025's Hottest Trading Products | OKX Year in Review
Looking at price action alone, it's hard to explain the returns gap between exchange users in 2025. What truly determines returns also depends on account-level trading methodology, not just market volatility itself. OKX's annual report shows that mainstream coins remain the core for capital turnover and returns, supporting trading and strategy execution; emerging coins are more used to amplify volatility and provide phase-based opportunities, but are not a stable, long-term source of returns. What truly and continuously contributes to returns is...
2025年12月30日

Fusaka in Practice: What Ethereum's Latest Upgrade Means for L2, Nodes, and Users
Ethereum mainnet has completed the Fusaka fork. At the protocol level, this upgrade primarily covers four areas. Read on for Q&A with More Show less: Three guests' core viewpoints and front-line experience: Ahmad (@smartprogrammer) – Nethermind Execution Client / Ethereum Core Dev Manu (@manunalepa) – Prysm / Of...
2025年12月16日

OKX Research | Why Did RWA Become a Key Narrative in 2025?
RWA (Real World Assets) is becoming the "new favorite" of global capital. Simply put, RWAs take valuable, ownership-bearing assets from the real world — such as houses, bonds, stocks, and other traditional financial assets, or even art, private lending, and carbon credits that aren't typically easy to trade directly — and bring them onto the blockchain, transforming them into tradeable, programmable crypto assets. This makes it possible to...
2025年11月20日
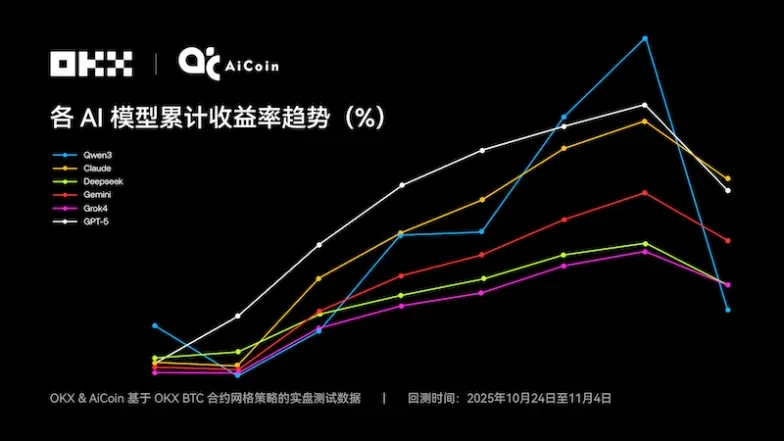
Claude Takes the Crown — 6 Major AI Grid Strategies Face Off | OKX & Ai Coin Live Test
Is the grid trading champion ? The first season of NOF1's "AI Trading Live Arena" finally concluded on November 4, 2025 at 6 AM, whetting the appetite of the crypto, tech, and finance communities. But the outcome of this "AI IQ open test" was somewhat unexpected — the combined $60,000 in starting capital across six models ended with only $4.3...
2025年11月6日